- Malik Logix
- Posts
- US Orders Air Force One
US Orders Air Force One
White House orders travelers on Air Force One to discard all Chinese-issued electronics and gifts following a high-stakes summit in Beijing.

Malik Farooq
May 15, 2026

Deep Dive

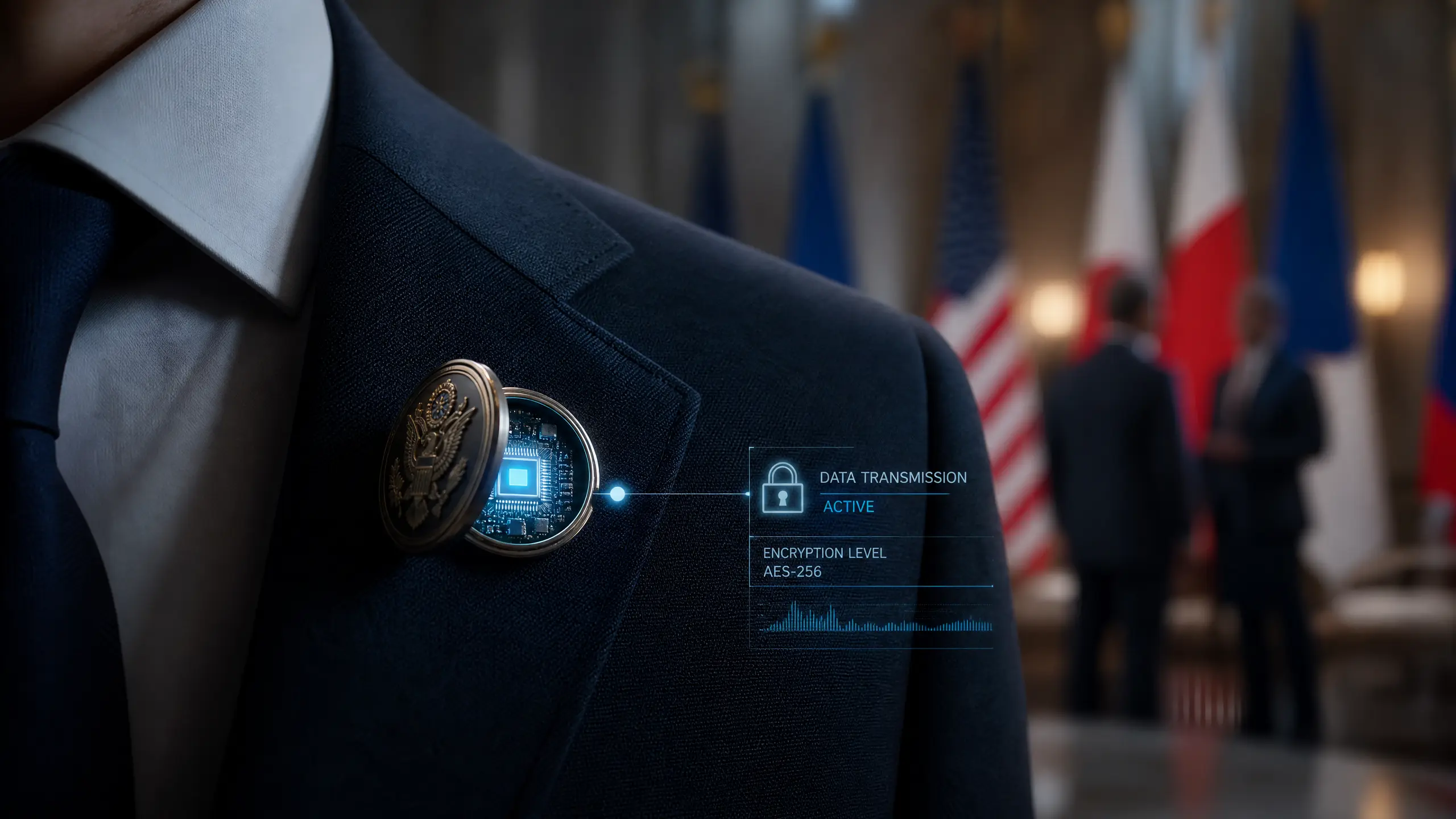
The High Stakes of Diplomatic Security: Why Air Force One Went "Dark" After China
The "Nothing from China" Rule
Why the Extreme Measures?
- Hardware Implants: Modern espionage often involves "bugging" physical objects. A lapel pin or a commemorative gift can easily house a micro-transmitter or a passive listening device.
- Supply Chain Vulnerabilities: Burner phones, while designed for temporary use, are prime targets for pre-installed malware or firmware-level backdoors.
- Credential Harvesting: Even a simple ID badge can contain NFC or RFID chips designed to track movement or attempt to bridge connections with other secure devices.
"In the world of high-stakes diplomacy, there is no such thing as a 'free' gift. Every physical object is a potential vector for a cyberattack." — Malik AI Security Insights
A History of "Trojan" Gifts
Practical Takeaways for Enterprise Security
- Device Sanitization: After high-risk travel, all devices should be wiped or replaced.
- Physical Security Audits: Be wary of unsolicited gifts or promotional items from unknown vendors.
- Burner Protocols: If using burner phones, ensure they are destroyed or securely recycled after their specific use case.
Statistics: The Rising Cost of Espionage
| Metric | Value |
|---|---|
| Estimated Annual Cost of IP Theft to US | $225B - $600B |
| Percentage of Cyberattacks Attributed to State Actors | 25% |
| Average Time to Detect a Sophisticated Breach | 212 Days |
Conclusion: A New Era of Vigilance
Ready to master AI?
Malik Logix is an AI Marketing and Newsletter Blog Site. Join us and spend 10 minutes a day to master AI Digital Marketing.
Join Free NowKeep reading

AI Hidden Minefield Trump China
Explore the complex AI landscape during Trump's China visit, focusing on the US-China AI race, military applications, and the challenges of global AI governance.

Android Enters Gemini Intelligence Era
Google unveils Gemini Intelligence for Android, integrating AI across devices with new Googlebook laptops and an AI-infused cursor, setting a new standard for mobile AI utility.

Microsoft Open-Source Toolkit Secures AI Agents
Discover how Microsoft's new open-source toolkit enhances runtime security for enterprise AI agents, addressing governance challenges and preventing unauthorized actions.